Securing the next generation of European digital identity and high-assurance infrastructure requires more than strategic planning; it demands a rigorous analysis of the mathematical foundations of our future trust models.
As part of the POSEIDON project’s mission to facilitate a robust transition to quantum-resistant ecosystems, this technical briefing provides the implementation-level detail necessary for architects, researchers, and those overseeing cryptographic migration.
This article presents the core concepts of post-quantum cryptography, situates it within the broader landscape of quantum-resistant cryptography, and examines its main families, practical uses, and security implications. By evaluating the specific computational problems—from lattice-based primitives to multivariate alternatives—we offer a comprehensive technical foundation for the experts tasked with maintaining institutional integrity in a post-quantum world.
Quantum-Resistant Cryptography: Different Approaches
Post-quantum cryptography and quantum cryptography are two major branches of what is often called quantum-resistant cryptography. In broad terms, quantum-resistant cryptography refers to methods of protecting information that are designed to remain secure even against attackers equipped with quantum computers.
The threat posed by quantum computing to modern cryptography is mainly associated with two well-known quantum algorithms: Shor’s algorithm and Grover’s algorithm. Shor’s algorithm can efficiently factor large numbers and solve related mathematical problems that are considered hard for classical computers. This is of fundamental importance because the security of widely used public-key systems: including RSA, Diffie–Hellman, and elliptic-curve cryptography, relies precisely on the difficulty of such problems. If a sufficiently powerful quantum computer became available, these systems could in principle be broken by recovering private keys from public information.
The advantage offered by Shor’s algorithm over the best-known classical methods is dramatic (exponential speedup), making it a serious long-term concern for public-key cryptography.
Grover’s algorithm affects a different class of cryptographic tools: symmetric encryption and hash functions. Unlike Shor’s algorithm, it does not break these systems outright. Instead, it speeds up brute-force search, effectively reducing their security level. In practice, this means that symmetric schemes can often remain secure in a quantum era, provided that key sizes are increased appropriately.
Divergent Security Paradigms: Physical Layer vs. Algorithmic Security
Quantum cryptography belongs to the domain of physical-layer security. Its purpose is not to encrypt data directly, but to enable the secure transmission of cryptographic keys from one point to another by exploiting the laws of physics.
These keys are then used to protect data with classical encryption algorithms, ranging from the theoretically ideal but highly impractical OTP (One-Time Pad) to the widely deployed and highly trusted AES (Advanced Encryption Standard). Such algorithms are called symmetric, because the same secret key is used by both the sender and the receiver, and the resulting cryptography is called private-key cryptography.
There is a fundamental difference between quantum cryptography and post-quantum cryptography. In fact, the difference is so profound that the two terms, although widely used, can be somewhat misleading when placed side by side.
The most important physical-layer security technique—and, in practice, the main representative of quantum cryptography—is Quantum Key Distribution. In QKD, cryptographic keys are established at the two ends of a communication channel using quantum states, typically involving single photons or other quantum effects associated with the transmission of light. Its distinctive feature is that security is rooted not in mathematical difficulty, but in the fundamental behavior of nature. However, despite its provable security, the fact that QKD relies on the physical transmission of quantum states makes it difficult to apply directly in many important areas, including digital identity.
Post-quantum cryptography, by contrast, belongs to the world of algorithmic, or digital, security. It does not rely on quantum phenomena at all. Instead, it aims to design classical cryptographic algorithms that can run on ordinary computers and networks yet remain secure even against attackers equipped with quantum computers.
Classical vs Post-Quantum Cryptography
When classical cryptography is compared with post-quantum cryptography, the discussion usually concerns public-key cryptography, or asymmetric cryptography, where public and private keys are distinct. Both traditional and post-quantum systems in this category rely on mathematical problems that are easy to compute in one direction but extremely difficult to reverse without secret information. In simple terms, they are based on computational puzzles that are easy to create but hard to solve. Their security rests on the assumption that, even with powerful computers, solving these problems remains infeasible within any practical time.
The computational problems underlying traditional public-key cryptography are typically based on number theory. One familiar example is the multiplication of two very large prime numbers: performing the multiplication is easy, but reversing the process, that is, determining which prime factors were multiplied together, is believed to be hard. This asymmetry lies at the heart of RSA, whose security is linked to the difficulty of integer factorisation.
Another important family of classical public-key systems is based on the discrete logarithm problem. In these schemes, it is easy to compute powers in a suitable mathematical structure, but hard to reverse the process and recover the exponent from the result. This idea underlies the Diffie–Hellman key exchange and also the DSA family of digital signature schemes.
A related but distinct approach is provided by elliptic-curve cryptography. Here, the relevant operation is not ordinary multiplication of numbers, but repeated addition of a point on an elliptic curve to itself, an operation usually called scalar multiplication. This process is efficient to carry out, yet hard to reverse: given two points on the curve, it is believed to be computationally infeasible to determine how many times one point was added to obtain the other. This is the elliptic-curve version of the discrete logarithm problem, and it forms the basis of elliptic-curve variants of Diffie–Hellman and digital signatures.
The Erosion of Traditional Computational Difficulty
For classical computers, the mathematical problems underlying traditional public-key cryptography are believed to be extremely hard, which is why they have long provided the basis for secure digital communication. In the quantum era, however, this assumption no longer holds. Shor’s algorithm shows that sufficiently powerful quantum computers could efficiently solve the factorisation and discrete-logarithm problems on which RSA, Diffie–Hellman, and elliptic-curve cryptography depend.
Symmetric cryptography is in a stronger position: although quantum search can weaken it, the effect is far less dramatic and can often be addressed by using larger key sizes. Recent advances in artificial intelligence have also stimulated discussion about new forms of cryptanalysis. Although the central scientific fact remains that the main disruptive threat comes from quantum algorithms, the broader search for cryptographic methods resilient to future AI-assisted attacks is an additional reason to strengthen our foundations.
This is why post-quantum cryptography has emerged: it seeks new cryptographic foundations based on mathematical problems for which no comparably powerful quantum attacks are known, and for which no general AI-based attacks are currently known either.
Five Main Forms of Post-Quantum Cryptography
Post-quantum cryptography is usually divided into five main families, according to the kind of mathematical problem on which security is based:
This five-family view is commonly used in overviews of post-quantum cryptography, and we will now briefly describe each family.
In each case, the explanation is intentionally simplified for teaching purposes.
- Lattice-based cryptography relies on problems involving points in high-dimensional grids called lattices. These structures are easy to generate, but some computational tasks on them are believed to be very hard, such as finding a very short vector or finding the lattice point closest to a given target point.
- Hash-based cryptography relies on the properties of cryptographic hash functions. A hash is easy to compute, but it is designed to be hard to reverse and hard to manipulate. In practice, hash-based signatures rely especially on the difficulty of finding collisions or forging authentication paths, rather than simply “inverting a hash.”
- Code-based cryptography is based on error-correcting codes, which are widely used in digital communication. The basic idea is that encoding data in a structured way is easy, but decoding a deliberately hidden random codeword without special secret information is believed to be hard.
- Isogeny-based cryptography uses special structure-preserving maps (functions), called isogenies, between elliptic curves. The mathematics is elegant and compact, but this family has become much less central after major cryptanalytic breaks of leading candidates. It is still part of the standard taxonomy, but today it is no longer among the main practical front-runners.
- Multivariate cryptography is based on systems of multivariate polynomial equations, usually quadratic ones. These systems are easy to compute in one direction, but solving them without secret information is believed to be hard.
More About Lattice-based Post-Quantum Cryptography
Among the different families of post-quantum cryptography, lattice-based cryptography is currently the most important in practice, because it forms the basis of the main standards now being adopted for digital signatures and key establishment.
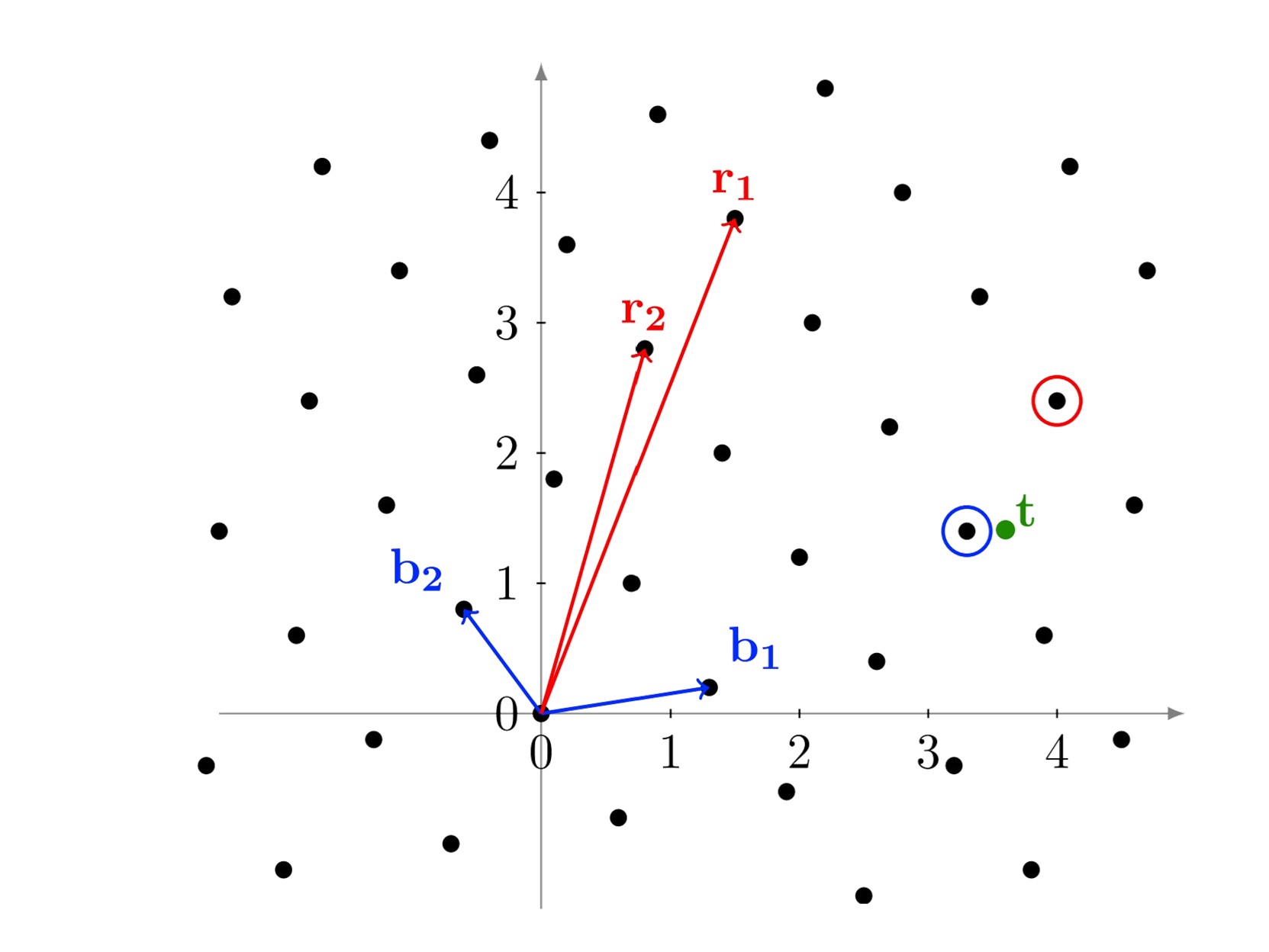
In lattice-based cryptography, security relies on the difficulty of certain computational problems on lattices. Two central examples are the Shortest Vector Problem (SVP), which asks for a shortest nonzero lattice vector, and the Closest Vector Problem (CVP), which asks for the lattice point closest to a target point t. In the figure below, the red vectors 𝑟1 and 𝑟2 define the lattice, while the blue vectors b1 and b2 illustrate a reduced basis of the same lattice. Although such problems are easy to visualise in two dimensions, they become extremely hard in the high-dimensional settings used in post-quantum cryptography.
Real lattice-based cryptography is built on problems involving very large grids of points in many dimensions, not two or three, but often hundreds or thousands. In such spaces, some tasks are easy to perform, while others, such as SVP or CVP or recovering a small secret from noisy data, appear to be extremely hard even for quantum computers. This asymmetry makes lattices a strong foundation for encryption and digital signatures.
Another reason for their importance is practical: lattice-based methods can be implemented efficiently on ordinary computers and are now at the heart of the leading post-quantum standards. In simple terms, lattice cryptography offers a rare combination of strong security, mathematical richness, and real-world usability.
However, despite the elegance and robustness of lattice-based cryptography, substantial effort is also being directed toward alternative post-quantum constructions. In the interest of mathematical diversity beyond lattice-based methods, NIST has promoted code-based cryptography as well; in particular, HQC has been selected as an additional post-quantum encryption standard, with final standardization expected in 2027.
Is post-quantum cryptography safe?
Unfortunately, no post-quantum algorithm can be proven absolutely secure in any practical sense. What can be said is that today’s leading post-quantum schemes have been studied extensively, and no efficient attacks are currently known that would break them in their intended security models.
By contrast, quantum cryptography, especially Quantum Key Distribution, offers a different kind of assurance: despite its fundamental deployment challenges, under specific assumptions, its security can be derived from physical principles rather than solely from unproven mathematical hardness assumptions.
For these reasons, many experts recommend hybrid approaches during the transition period, combining post-quantum methods with established classical ones so that security does not depend on a single family of algorithms. Until post-quantum cryptography is fully deployed and confidence in long-term implementations grows, hybrid protection is widely seen as the most prudent path forward.
Collaborating on Quantum-Resistant Foundations
The transition to a post-quantum landscape requires more than just theoretical knowledge; it necessitates rigorous technical validation and cross-sector collaboration. Within the POSEIDON project, we are actively evaluating the performance, security, and implementation challenges of the cryptographic families discussed in this article. Our goal is to ensure that the mathematical foundations of European digital identities and high-assurance infrastructures are not only quantum-resistant but also optimised for real-world deployment across diverse digital ecosystems.
To stay informed about our deliverables, research findings, and contributions to international standardisation, we invite you to subscribe to our newsletter and follow the POSEIDON project on LinkedIn. We also welcome engagement from experts, researchers, and organisations involved in cryptographic migration; if you are interested in collaboration or have specific inquiries regarding our research, please reach out to us directly.

Dr Mirek Sopek
Quantum Blockchains